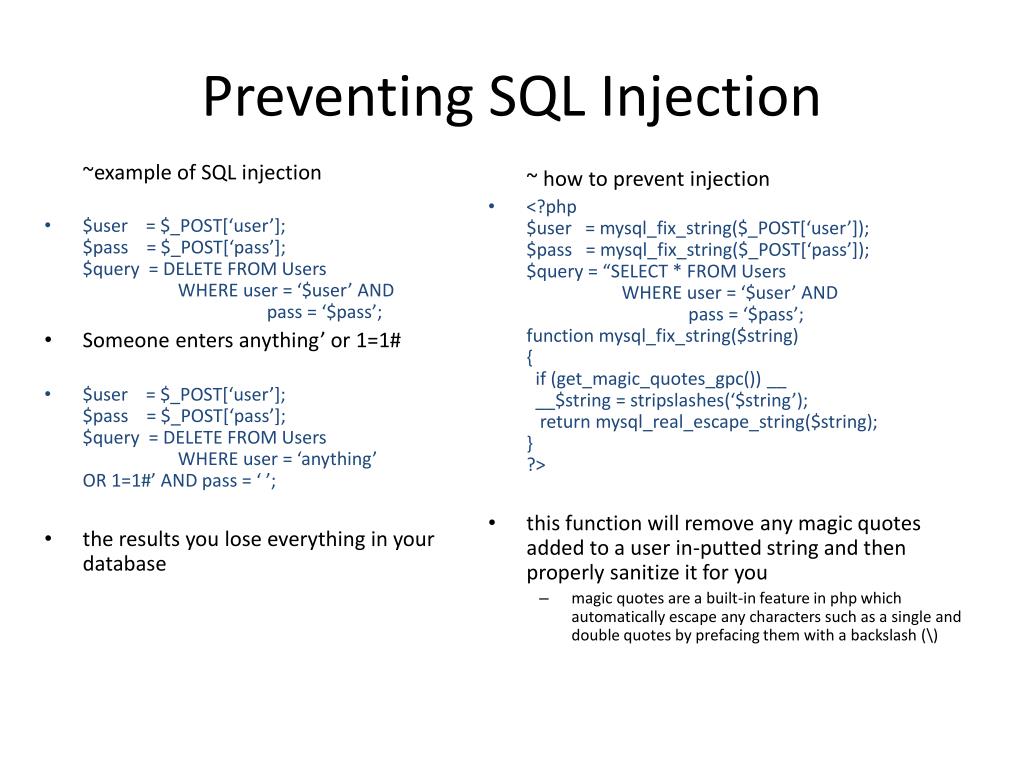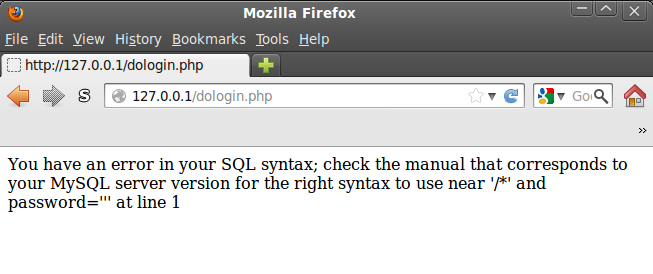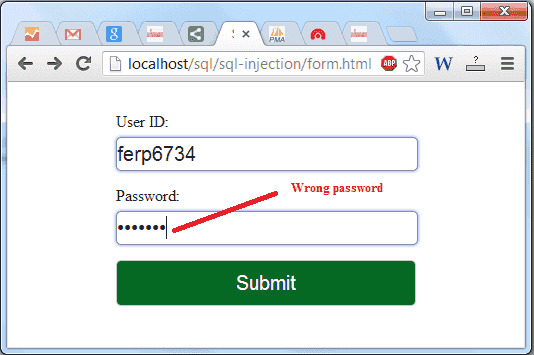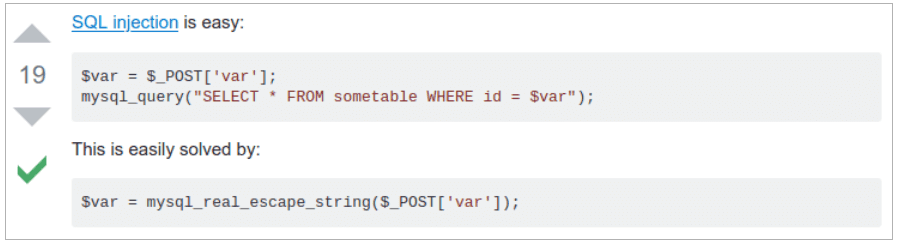
SQL injection as one of the biggest vulnerabilities for your data - Security | Larapulse Technology Blog

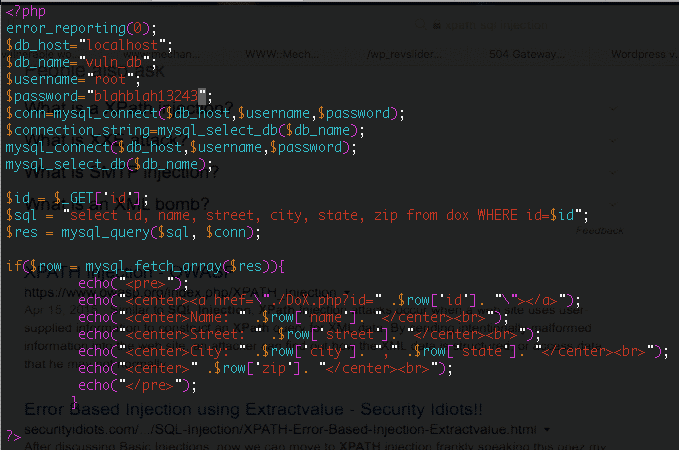
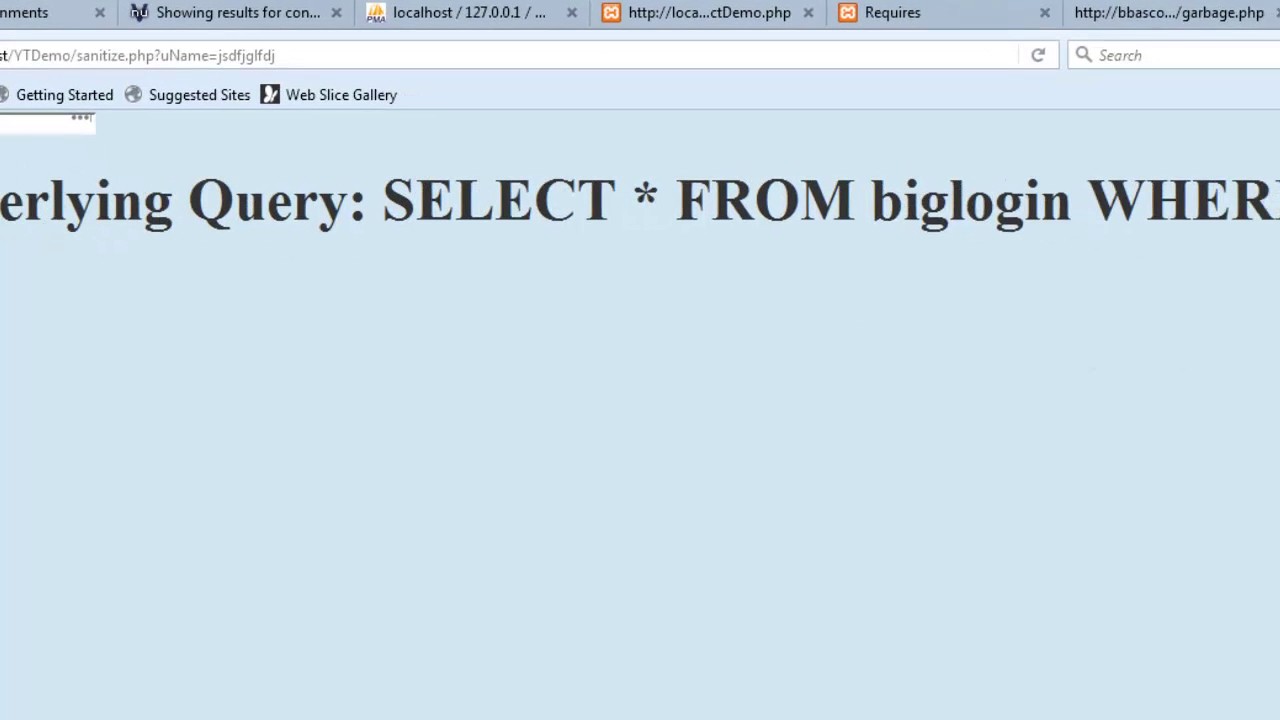
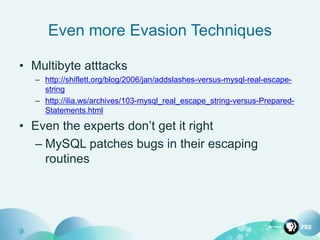
Finding an unseen SQL Injection by bypassing escape functions in mysqljs/ mysql | by Flatt Security Inc. | Medium

mySQL_real_escape_string() It can be seen in the Table 6 that it is not... | Download Scientific Diagram


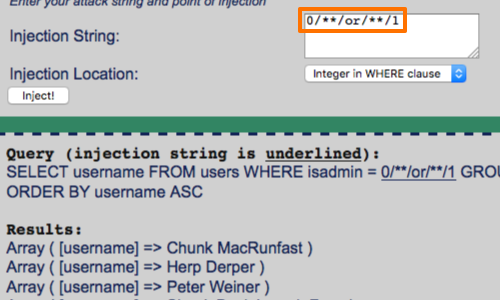
![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/IzT7BKf4tQ8/maxresdefault.jpg)